What x402, Agentic Wallets, AP2, MCP/A2A, and ERC-8004 Mean for Agentic Web3 Careers
This page explains what x402, agentic wallets, AP2, MCP/A2A, and ERC-8004 mean for agentic Web3 careers. If you are trying to understand where this stack touches real jobs, hiring, and proof of work, the useful question is not which term sounds newest.
The useful question is what these layers change about real roles and real systems.
The stack is moving beyond AI that only suggests. More systems are being designed around agents that can use tools, coordinate tasks, trigger payments, and interact with wallet or on-chain infrastructure under defined controls. Once that happens, the work changes. Backend work changes. Wallet and infrastructure work change.
Product decisions change. Security thinking changes. Hiring changes too, because teams stop caring only about whether you sound current. They start caring about whether you understand execution, permissions, trust, monitoring, and proof.
This guide translates that shift into career language. It will show what each layer changes, which existing role families it is reshaping, what hiring teams are likely to verify first, and how to make your proof easier to trust if you want to work in this lane. For the broader evaluator lens behind this article, start with proof-based hiring in Web3 and Web3 hiring signals.
TL;DR
These terms matter because they change job scope, not just architecture diagrams.
The strongest role families here are still familiar ones: backend, platform, wallet infrastructure, security, product, and solutions architecture.
The real shift is not “AI is everywhere.” The real shift is that systems are becoming more action-capable, payment-aware, and control-sensitive.
Hiring teams will care less about whether you can repeat protocol names and more about whether you understand permissions, payment logic, trust, monitoring, and failure handling.
The strongest candidates in this lane will not just sound informed. They will show readable proof of good judgment.
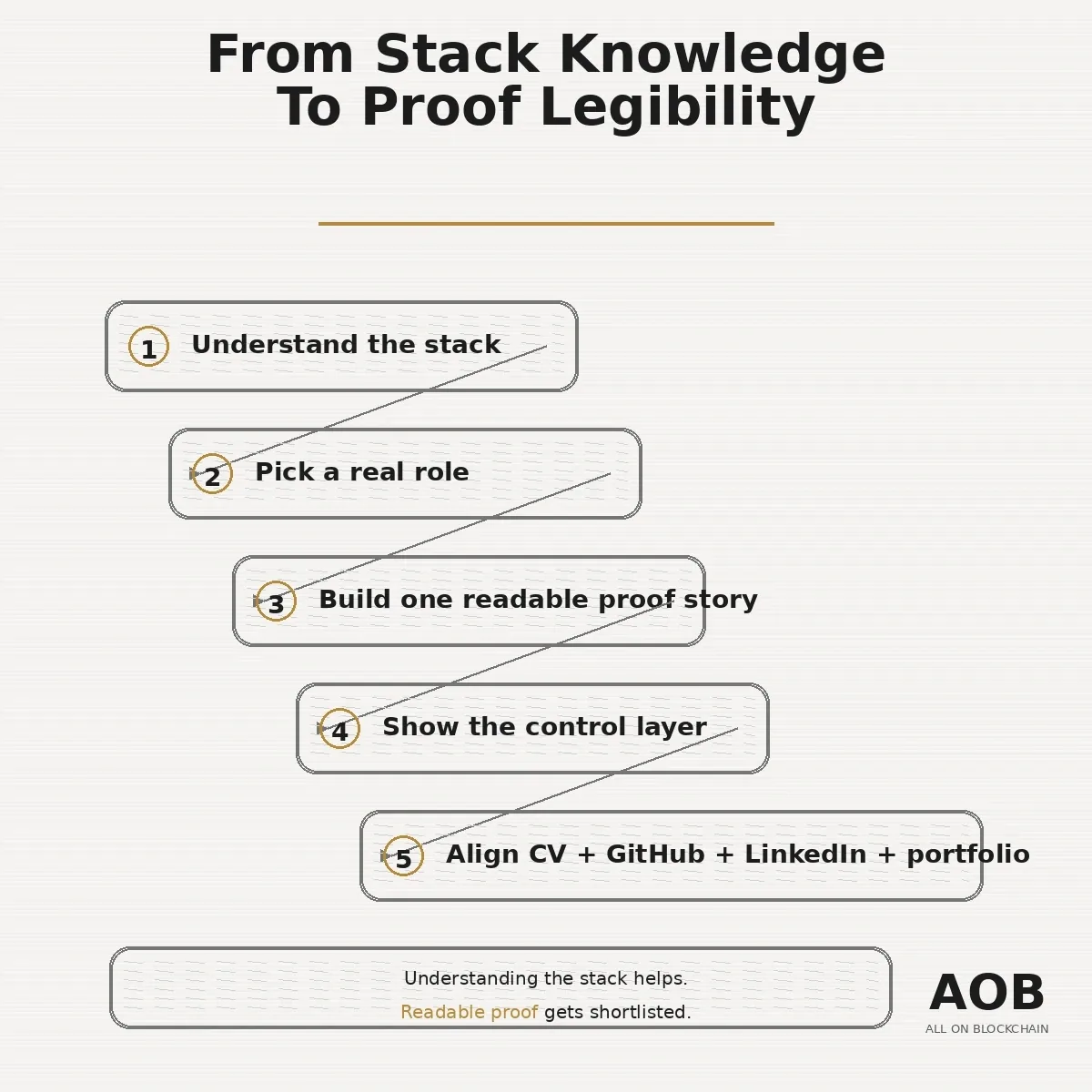
The goal is simple: understand the stack, then make your proof legible.
Why this matters for careers
This is not just new vocabulary for the same old work.
The moment agents move closer to execution, the work starts spilling across boundaries that used to feel separate. A backend engineer may now need to think about payment-trigger logic and access after payment. A wallet engineer may need to think more deeply about approvals, limits, and override paths. A product manager may need to define where automation ends and human approval begins. A security-minded candidate may need to show not only how something works, but how it stays safe when an agent can act.
That is why this topic matters more as a careers and hiring question than as a trends question.
The useful question is not whether AI and blockchain are converging in theory. The useful question is what that convergence changes about:
Role design
Execution responsibility
Proof of work
Evaluator logic
Hiring signals
That is where the real value sits. If you want a sharper hiring-side companion to that idea, read how recruiters can hire smarter in Web3.
What these terms change in real jobs
The easiest way to read this stack is not as a glossary. Read it as a set of layers that change what teams build and what candidates need to prove.
x402
x402 matters because it brings payment closer to the application layer.
Instead of treating payment as a separate checkout moment, it points toward a model where payment can sit inside a machine-readable request-response flow. For career seekers, that matters because it makes payment logic feel more like infrastructure work and less like a disconnected commerce feature.
What x402 changes in practice:
a paid API is no longer just a billing problem; it becomes part of the service flow
machine-to-machine payments start feeling more practical
access after payment becomes a systems question, not just a UX question
backend roles start touching verification, settlement, and payment-aware logic more directly
For jobs, the value of x402 is not “I know the term.” The value is being able to explain how payment logic, service access, and verification start blending inside real systems.
Agentic wallets
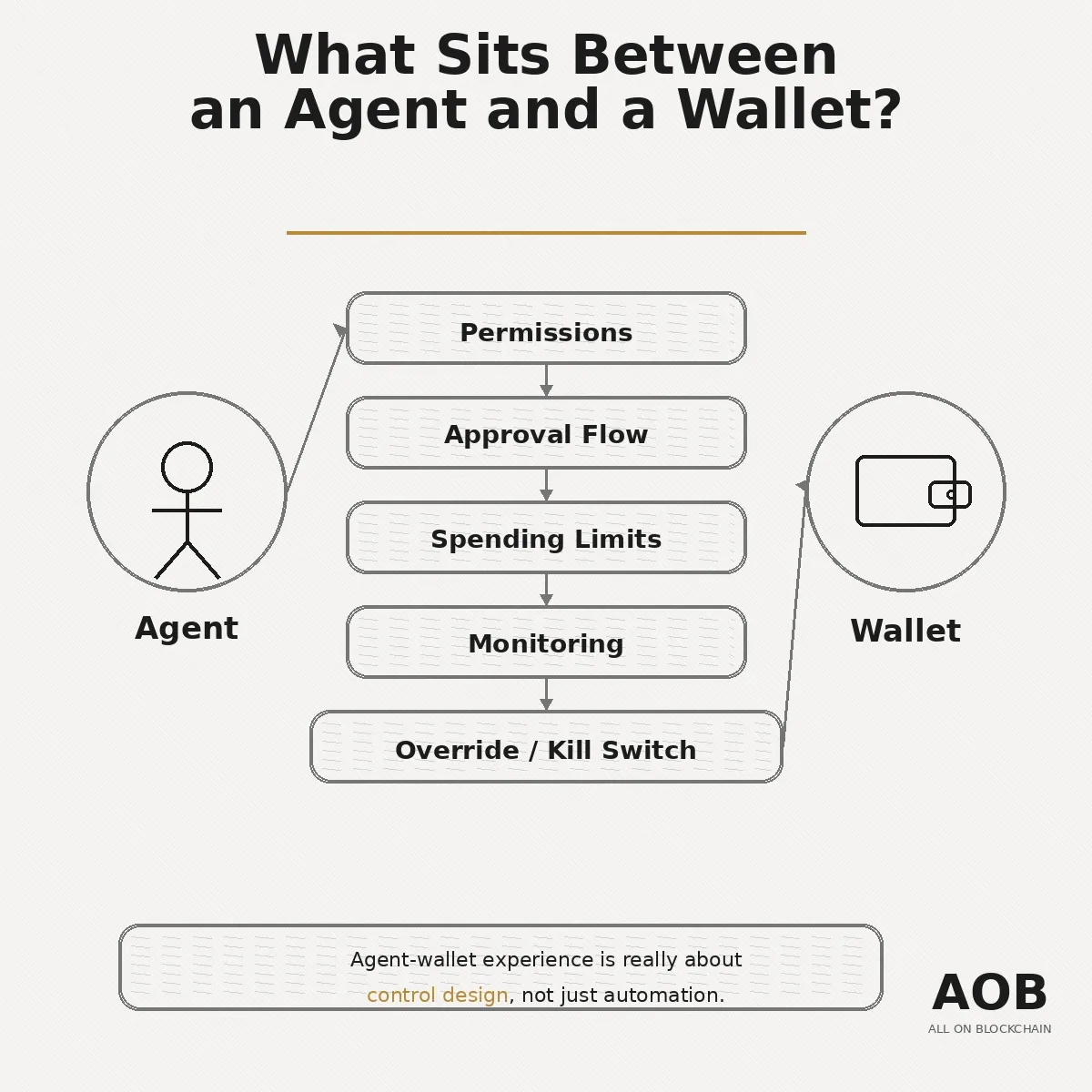
“Agentic wallet” sounds futuristic, but the useful career lens is much more practical.
The real question is not whether an agent can touch a wallet. The real question is what sits between an agent and spend authority.
That turns the conversation into real infrastructure questions:
What permissions are granted
What actions require approval
What the spending limits are
What gets monitored
What can be paused, reviewed, or revoked
That is why this layer matters so much for wallet infrastructure, trust-heavy backend work, security thinking, and risk-aware product design.
If someone claims agent-wallet experience, hiring teams will trust that claim more when they can see control thinking, not just wallet automation language.
MCP and A2A
These two terms are often mentioned together, but they solve different problems.
A clean way to think about them:
MCP is about reaching tools, data, and workflows
A2A is about coordination between agents or services
That distinction matters because roles often lean more toward one side than the other.
If a role is closer to structured workflow execution, tool access, or system context, MCP-style thinking becomes more useful. If a role is closer to delegation, orchestration, handoffs, or collaboration across systems, A2A-style thinking becomes more relevant.
For jobs, this changes the value of backend, platform, infrastructure, and product roles. Teams will care more about whether someone can reason about execution pathways, not just outputs.
AP2
AP2 is useful context, but it should stay in proportion.
For most readers, it is best understood as part of the broader move toward agent-aware payment systems rather than as a mature standalone career lane. It helps signal where payment design is going, especially around agent-led transactions and secure payment flow, but it is still not the kind of label most people should build their whole positioning around.
What AP2 changes in practice:
payments become more agent-aware
authorization and transaction flow matter more
commerce-linked product and backend work need clearer guardrails
payment judgment becomes more important than payment integration alone
That makes AP2 relevant as stack literacy, especially for payments-adjacent roles, but not strong enough yet to become the center of a career story.
ERC-8004
ERC-8004 matters because communication and execution are not enough by themselves.
If agents are going to operate across systems or organizations, teams also need ways to think about identity, discovery, validation, and trust. That is what makes this layer interesting for career readers. It introduces trust-heavy thinking into a stack that might otherwise sound purely operational.
What does that work changes:
trust becomes part of architecture, not just policy
Monitoring and validation matter more
discovery and identity become part of system design
Security-minded evaluation becomes more important
This matters because trust-heavy systems usually create trust-heavy hiring filters.
How the stack fits together
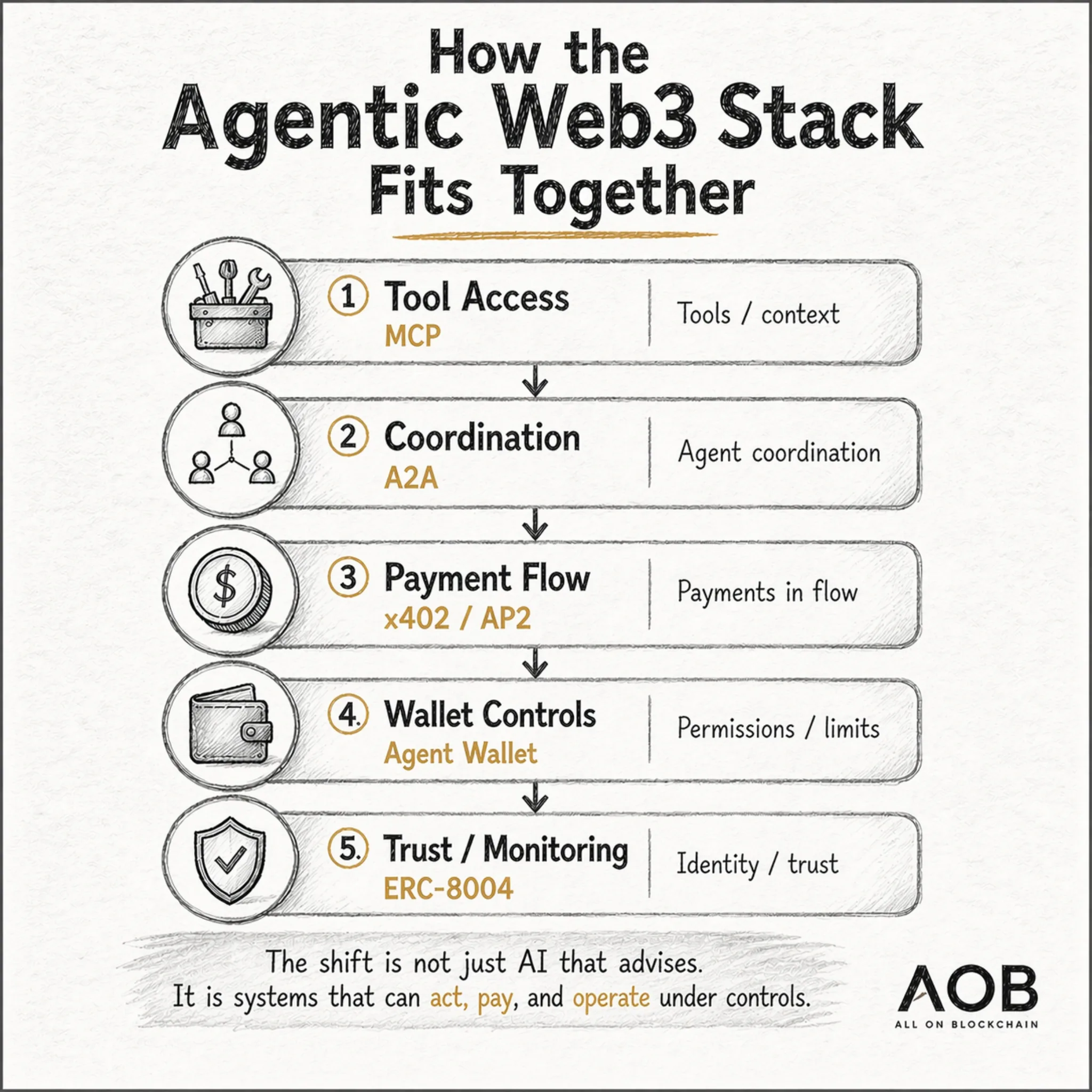
An agent usually does not “use x402” or “use MCP” in isolation.
In practice, the flow is closer to this:
The agent gets tool access
it decides or delegates work
it triggers an action
it passes through payment or wallet controls if value is involved
it operates under trust and monitoring constraints
That means the stack is easier to understand as five working layers:
Tool layer: expose systems and workflows safely to agents
Coordination layer: let work move across agents or services
Payment layer: attach value movement to machine-readable flows
Wallet and permissions layer: enforce approval logic, limits, and overrides
Trust and monitoring layer: decide what should be trusted, observed, paused, or validated
This matters because careers are shaped by where someone owns risk, control, and decision quality inside that flow.
Which existing roles is this stack reshaping
Most companies will not hire with perfect “agentic” job titles yet.
They will hire through familiar roles and then expand the scope to include tool access, payment logic, wallet permissions, trust, and monitoring. That is the more realistic lens for readers too: start with the role family employers already recognize, then show how the newer stack changes the work.
If you want to compare this article against live demand, browse blockchain developer jobs. It is a better reality check than trying to guess which new labels will win.
Backend engineer
This is one of the clearest entry points into the career path.
What changes for backend engineers:
More work around verification and workflow execution
Payment-trigger logic becomes more relevant
Service orchestration matters more
Access control and post-payment behavior become more important
What believable proof looks like:
Payment-aware APIs
Readable workflow logic
System behavior that shows execution control
Clear thinking around verification and failure paths
Platform or infrastructure engineer
This role family becomes more important when the system itself is the product surface.
What changes here:
Exposing tools safely becomes more important
Orchestration reliability becomes part of the job
Observability and boundaries between services matter more
Execution-path reliability becomes a real hiring signal
What believable proof looks like:
Monitoring design
Integration surfaces
Execution-path clarity
Readable infrastructure choices
Wallet engineer or wallet infrastructure engineer
This is probably the most natural Web3-specific role family in the whole article.
What changes here:
more attention to permissions
more design around approval flows
more thinking around spend limits and transaction-control logic
more focus on monitoring and safe execution
What believable proof looks like:
Policy boundaries
Wallet behavior design
Monitoring hooks
Safe execution thinking
Clear answers to what sits between an agent and spend authority
Security engineer
Once agents can trigger actions, touch wallets, or initiate payment-linked workflows, the security lens becomes much more practical.
What changes here:
More attention to permission abuse
More thinking around unsafe automation
Misuse prevention becomes more visible
Failure containment matters more
What believable proof looks like:
Threat thinking
Approval logic
Control design
Monitoring choices
Clear reasoning about how something stays safe when automation has consequences
Product manager
This lane will not be engineering-only.
What changes for product roles:
Approval paths become more central
User-intent boundaries matter more
Fallback logic becomes part of product thinking
Trust tradeoffs become more visible
Accountability around who can do what becomes more important
What believable proof looks like:
Workflow design
Specs that show control thinking
Trust-aware product decisions
Clear decision-making around limits, review, and escalation
Solutions architect or technical solutions engineer
This role family matters when the work sits across systems, implementation, partner workflows, and control points.
What changes here:
Payment flow and trust boundaries become more important
Integration design becomes more control-sensitive
Oversight needs to be made explicit
System mapping matters more than polished language
What believable proof looks like:
Architecture maps
Integration planning
Clear reasoning around control points
Readable tradeoff decisions
Who transitions well into this lane
This lane is often a strong fit for:
Backend engineers who already think in workflows and verification
Payments engineers who already understand movement of value
Platform / DevOps engineers who already think in controls and reliability
Security engineers who already think in policy and misuse prevention
Wallet / infra builders who can reposition around permissions and safe execution
The titles may stabilize later than the work itself. But the responsibility patterns are already becoming easier to recognize. For the broader proof-first frame behind that idea, read proof-based hiring in Web3.
What hiring teams will actually verify
This is where the topic becomes commercially useful.
Hiring teams will not verify this lane by asking whether a candidate can repeat protocol names. They will verify it by looking for signs that the candidate understands payments, permissions, trust, monitoring, and safe execution in practice.
If you want the deeper evaluator lens after this section, read proof-heavy smart contract portfolios and how recruiters read your GitHub.
They verify proof of work, not protocol fluency
Knowing the vocabulary may get attention. It does not reduce hiring risk by itself.
What hiring teams actually look for:
evidence that you understand what changes when an agent can act, pay, sign, or touch wallet-linked infrastructure
signs that you can reason about permissions, approval flows, and limits
proof that you think about failure states, monitoring, and misuse prevention
artifacts that make your experience readable fast
work that matches the role you are claiming, not just the trend you are referencing
In wallet-related work, they verify control thinking
A weak candidate says they worked on wallets or agent-wallet flows.
A stronger candidate makes these things visible:
what sat between the agent and spend authority
how approval logic worked
how permissions were bounded
what could be paused, flagged, reviewed, or revoked
how safe execution differed from successful execution
In payments-related work, they verify judgment
A weak candidate talks about payment integration.
A stronger candidate can explain:
Payment-trigger logic
Verification and settlement flow
Access after payment
Trust assumptions around payment-linked action
The difference between a demo and a production-like responsibility surface
In GitHub and portfolio artifacts, they verify readability
A strong proof stack makes the evaluator’s job easier.
What that usually looks like:
The role story is obvious
The artifact shows how the system behaves
Documentation explains why key control decisions were made
Trust, permissions, payments, or monitoring are visible
A non-deep-technical reviewer can still grasp the hiring signal
Red flags appear faster than candidates expect
Repeating protocol names without implementation judgment
Claiming wallet experience without discussing permissions or monitoring
Claiming payment experience without verification or trust thinking
Showing a flashy demo with no guardrails or failure handling
Using broad “AI + blockchain” positioning instead of a clear role story
The real hiring question is simple:
Can this person be trusted with payment-aware execution, control-sensitive systems, and readable decision quality?
A good hiring-side companion to this is how recruiters can hire smarter in Web3.
How to make your proof legible for agentic Web3 roles
Understanding the stack helps. It does not automatically make you shortlist-ready.
The next step is not more vocabulary. The next step is making your proof readable — in your CV, portfolio, GitHub, and role positioning.
Start with a real role
Do not begin by building your identity around five protocol names.
Begin with a role family the market already recognizes, then make your proof support that role.
Backend engineer: show workflow logic, APIs, verification, and payment-aware execution
Wallet or wallet infrastructure engineer: show permissions, limits, approval paths, and monitoring
Platform or infra engineer: show system boundaries, orchestration, observability, and safe execution
Security engineer: show threat thinking, misuse prevention, policy logic, and containment
Product manager: show approval design, trust tradeoffs, accountability logic, and clear user-intent boundaries
Make your artifacts tell the same story
Your CV, GitHub, LinkedIn, portfolio, and project explanations should all tell the same story.
Strong proof should make visible:
role clarity
control thinking
artifact quality
recruiter readability
alignment
A reviewer should be able to understand the signal quickly.
If your proof still feels vague, start with blockchain CV review: what recruiters reject in 10 seconds and the smart contract portfolio that shows how you think.
The shortest formula for strong proof in this lane
pick a real role
show one readable proof story
make the control layer visible
use protocol names only where they help explain the work
keep the whole profile aligned to the same hiring signal
Where this lane is still early — and what not to overclaim
This page should also protect reader trust.
Not every new term will turn into a stable hiring lane at the same speed.
What this page will not help you do:
it will not teach every protocol deeply
it will not replace role-specific GitHub or portfolio proof work
it will not replace CV positioning
it will not turn early vocabulary into instant job-title maturity
What it will help you do:
understand the stack well enough to position yourself credibly
identify which existing role family you fit
understand what hiring teams verify first
move toward stronger proof and clearer positioning
That matters because early markets reward readers who are grounded, not just early.
FAQ
What does x402 mean for jobs in Web3?
For career readers, x402 matters less as a protocol label and more as a signal that payment can move closer to the application layer. That makes it more relevant for backend, payments, infrastructure, and monetization-aware product work. If you claim exposure here, hiring teams will care more about your thinking around verification, payment-trigger logic, and access after payment than whether you can define x402 from memory.
What are agent wallet roles?
Agent wallet roles usually sit inside existing job families such as wallet engineering, wallet infrastructure, backend systems, product, or security. The important work is rarely “agent wallet” in isolation. It is usually about permissions, approval flows, spend limits, monitoring, and safe execution.
Are agent payments new roles or renamed backend jobs?
Right now, they are often existing backend, payments, or infrastructure roles with a changing scope. Some companies may introduce newer labels over time, but most hiring still happens through familiar titles first. What changes is the responsibility surface: more payment-aware execution, more trust assumptions, and more need for readable proof.
Do I need smart contract experience to work in this lane?
Not always. This lane can fit backend engineers, platform engineers, wallet or infra builders, security engineers, product managers, and solutions architects. Smart contract knowledge can help, but many roles here are still shaped more by systems thinking, controls, trust, and execution design than by contract writing alone.
What should recruiters verify in candidates claiming agent-wallet experience?
They should verify whether the candidate can explain:
what sits between the agent and spend authority
how permissions were bounded
what approval logic existed
how monitoring and overrides worked
how failure handling was designed
That usually tells you more than the label itself.
What counts as real experience in agent payments?
Real experience usually looks like more than a payment demo or protocol name-drop. It looks like work that shows payment-trigger logic, verification, settlement awareness, access after payment, trust assumptions, and role-relevant system judgment.
Can backend engineers move into agentic Web3 roles?
Yes, often more naturally than they think. Backend engineers already understand APIs, workflows, verification, system boundaries, and execution logic. The shift is usually not into a completely new identity, but into a more payment-aware, wallet-aware, and trust-sensitive version of work they may already know.
Are AP2, MCP/A2A, and ERC-8004 real career keywords yet?
They are useful stack vocabulary, but most candidates should treat them as support language, not as the center of their positioning. The stronger move is to anchor yourself in a real role family, then use these terms only where they help explain the work you have done.
CTA
Understand the stack, then make your proof legible.
If your current CV, GitHub, or LinkedIn still sounds broad, trend-led, or hard to verify, the next step is usually not more theory. It is clearer proof, stronger positioning, and better matching between your work and the role you want. That is exactly where Web3 CV review services become useful.
If you are hiring instead of applying, job description review service for Web3 hiring teams is the cleaner next step.