Smart Contract Audit Checklist: What Auditors Actually Check (and How to Prepare)
<?xml encoding="UTF-8">
If you’re shipping a Solidity contract, an “audit” isn’t a badge — it’s a repeatable security process that reduces the chance of one bug turning into a headline. Most teams don’t fail because they didn’t run tools.
They fail because the logic assumptions were wrong, a privileged role was too powerful, an integration behaved differently in production, or an upgrade path wasn’t protected the way everyone assumed.
This guide is intentionally practical: what auditors actually check, a simple pre-audit checklist you can run before spending money, how to read an audit report without false confidence, and (if you’re career-curious) how people build proof for Web3 security roles without relying on “certificates only.”
If you’re preparing for audit/security interviews, keep this open too:
Smart Contract Interview Prep Hub:
https://artofblockchain.club/discussion/smart-contract-interview-prep-hub
TL;DR: Smart Contract Audits (Checklist + Career Path)
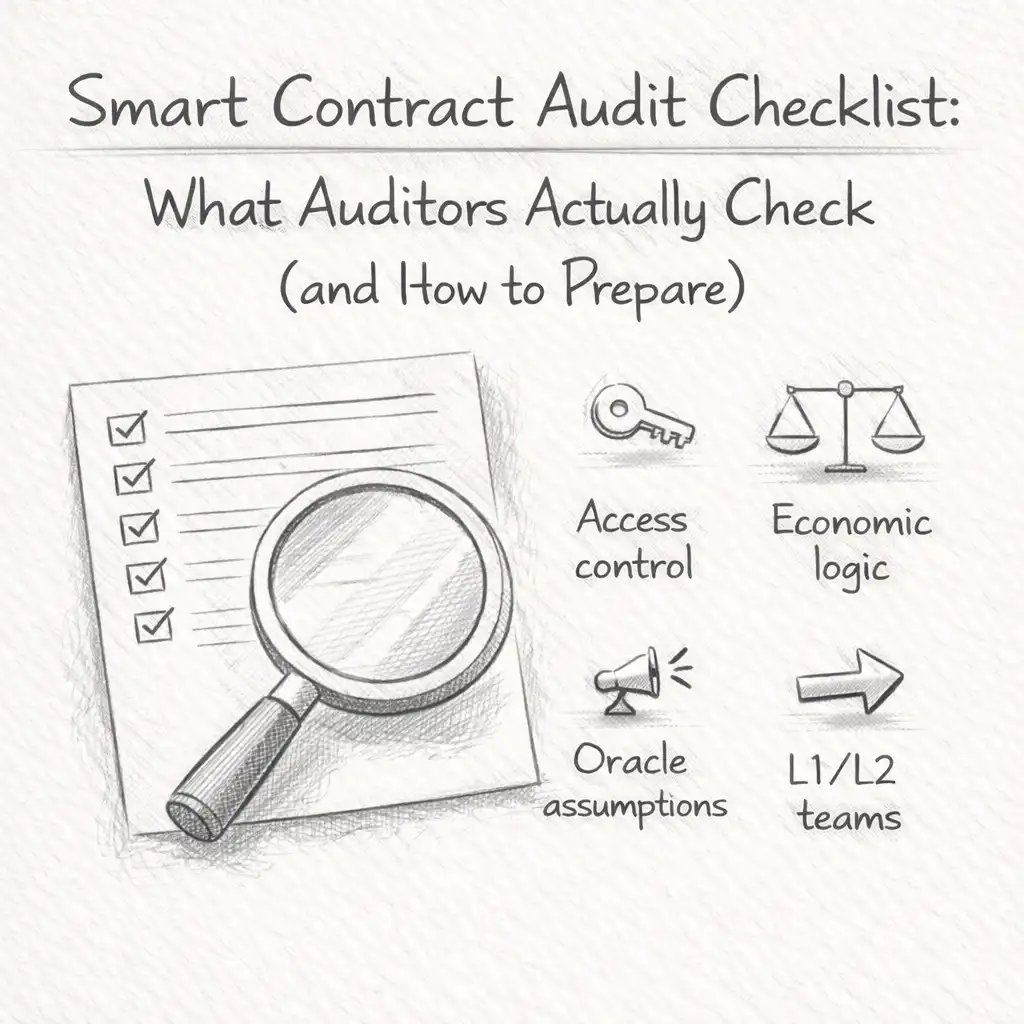
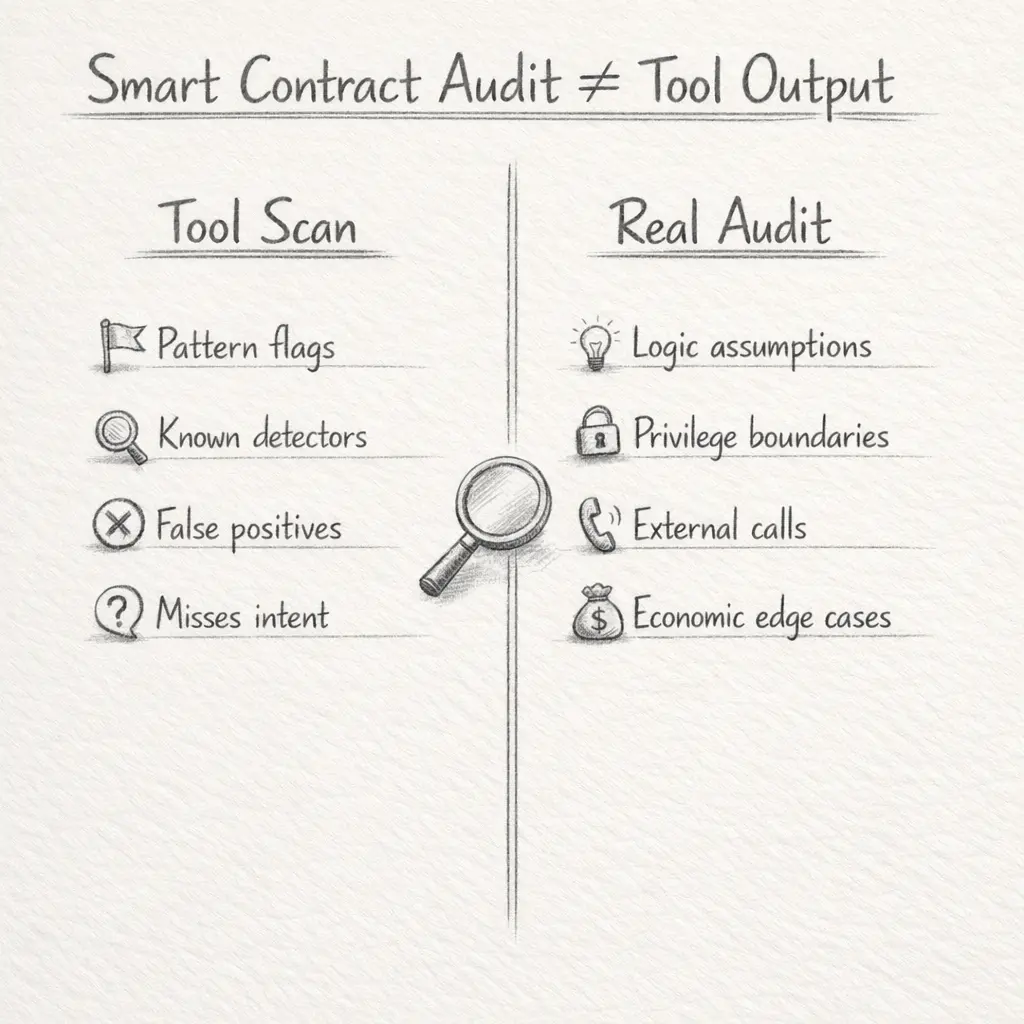
A real audit is not “tool output.” It stress-tests assumptions: privileges, upgrade safety, external calls, and economic logic.
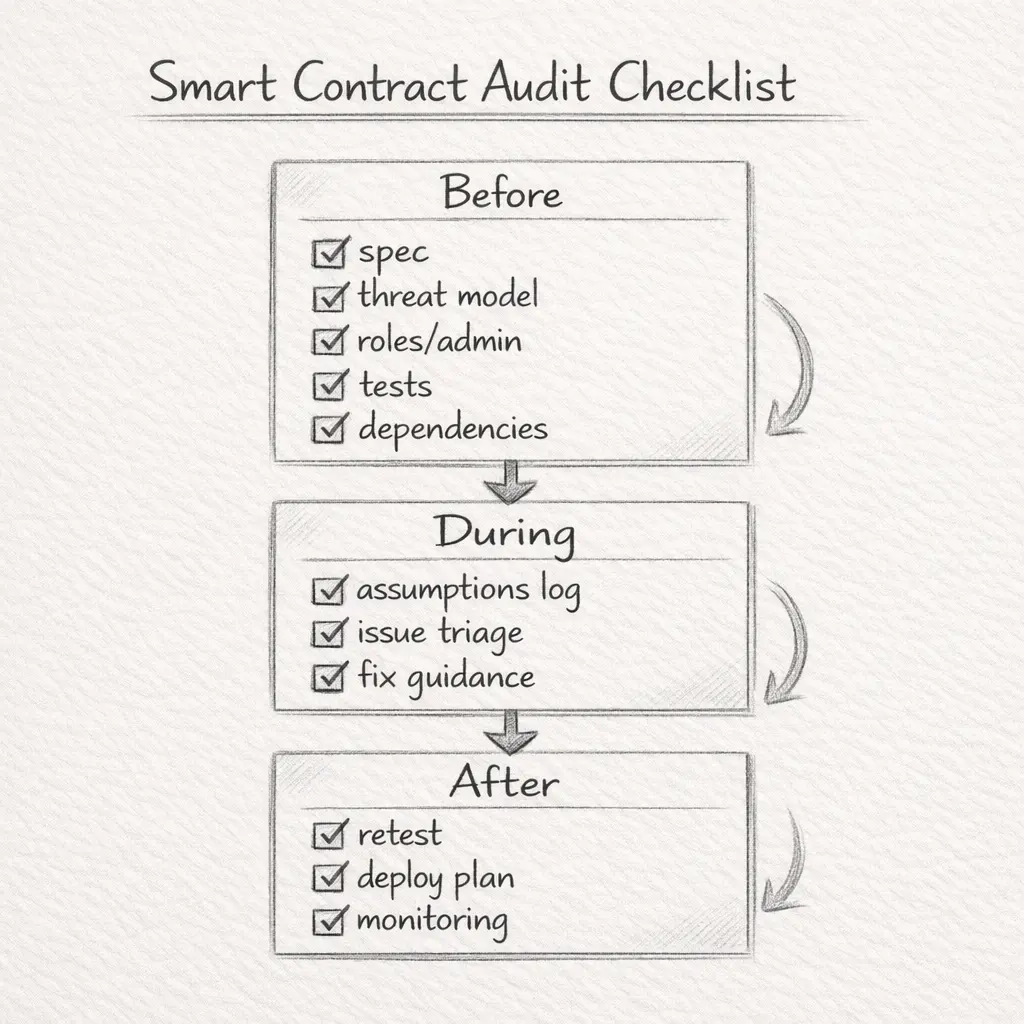
Pre-audit checklist matters: spec + threat model + roles/admin model + tests + dependencies + a retest plan.
Tools help (Slither/Echidna/Foundry), but manual review catches the dangerous “looks fine” bugs.
Audit reports: severity labels aren’t the truth — check exploitability + impact + likelihood + whether a retest happened.
Career angle: auditing is “proof-first.” Writeups, contest history, and clean repos usually matter more than certifications.
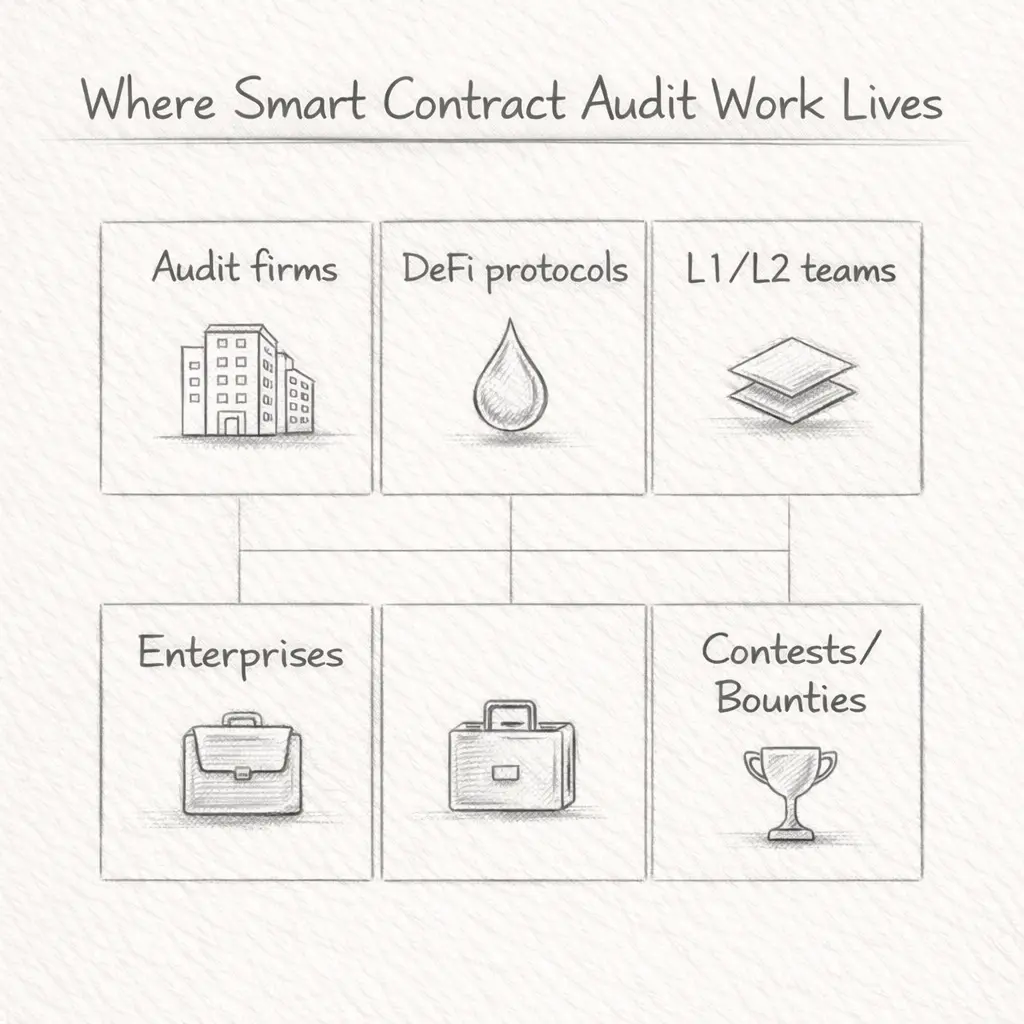
Hiring is broad: audit firms, DeFi protocols, L1/L2 teams, enterprises, and contest/bounty ecosystems.
The State of Blockchain Talent Demand in 2025
Web3 hiring moves in cycles — but security work doesn’t pause. Protocols keep shipping upgrades, new integrations keep getting added, and attackers keep watching for small mistakes that become systemic failures. That’s why security and protocol-heavy roles stay consistently relevant, even when “growth roles” slow down.
What’s changed in the last couple of years is the expectation bar. Many teams now want people who can do more than “ship contracts.” They want engineers who can reason about adversarial behavior, understand integration risk, and write tests that reflect real failure modes.
If you’re new and want a realistic view of how people enter the space, this discussion is useful:
From QA engineer to blockchain security auditor: https://artofblockchain.club/discussion/from-qa-engineer-to-blockchain-security-auditor-which-skills-help-most
And if you’re curious how QA fits inside audit workflows (underrated), read:
QA testers during smart contract audits:
Top High-Paying Blockchain Roles (Beyond Auditing)
Smart contract auditing is a strong path — but it’s not the only role that pays well or stays resilient. Here are a few roles that consistently show up in serious teams:
1) Smart Contract Auditor / Security Researcher
Focus: code review, adversarial thinking, exploit paths, clear reporting, retests.
Comp: varies widely by team + reputation + payouts (bounties/contests can add upside, but shouldn’t be your only plan early on).
2) Protocol Engineer
Focus: consensus/scaling/infrastructure, integrations, performance and correctness under load.
This is closer to “systems engineering,” and teams often test deep fundamentals here.
3) Web3 / Full-Stack Developer
Focus: dApp frontends + smart contract integration, signing flows, wallets, indexing, transaction lifecycle.
4) Blockchain Developer (Entry–Mid)
Focus: smart contract features, integrations, tests, and maintaining production code.
If you’re confused by role titles (developer vs engineer), this discussion helps:
Blockchain Developer vs Blockchain Engineer: https://artofblockchain.club/discussion/blockchain-developer-vs-blockchain-engineer
Top High-Paying Blockchain Roles
Why these roles get paid (and why “proof” matters)
When people think of “Web3 jobs,” they usually picture only devs or auditors. In reality, pay tends to follow blast radius — how expensive mistakes become in production.
Auditors/security researchers reduce the odds of catastrophic losses and reputation collapse.
Protocol engineers decide whether systems scale or fail under stress.
Full-stack Web3 devs own user-facing trust: signing flows, transaction safety, and integration correctness.
Entry-level devs are the pipeline — and the fastest growers are the ones who build proof early (tests, writeups, repos).
If you’re aiming for security, treat your public work like a portfolio — not like homework you hide.
Why Smart Contract Auditing is a Key Niche
Smart contracts move real value. That means small mistakes don’t stay “small.” A missed access control check, a reentrancy surface, or a broken assumption about an external dependency can turn into fund loss, frozen withdrawals, or upgrade disasters.
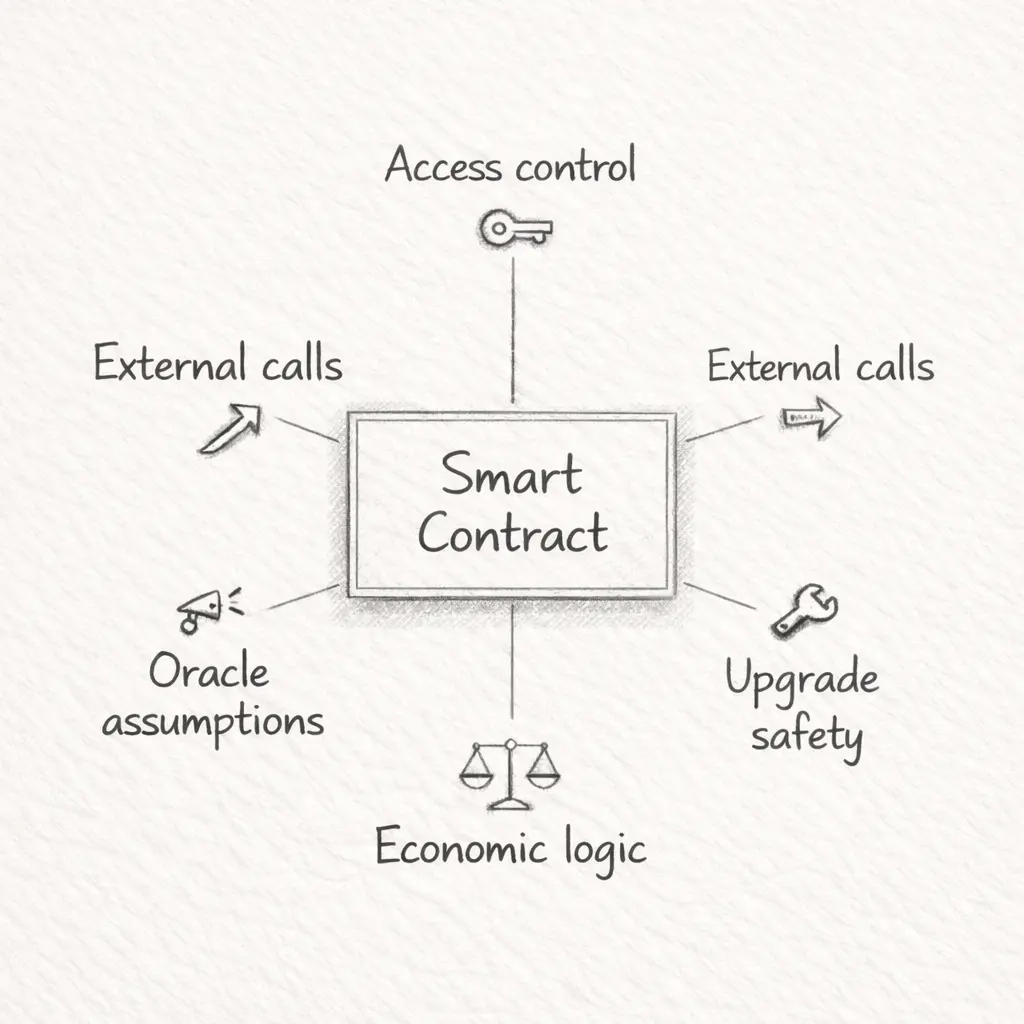
What many people miss: auditors don’t only look for textbook bugs. They check things like:
Privilege boundaries: who can pause, upgrade, withdraw, set fees, or change critical parameters
External calls: how value and control flow behave around token callbacks, routers, hooks, and integrations
Upgrade safety: whether upgrade paths are protected and monitored, and whether storage layout assumptions hold
Economic logic: whether incentives break under edge cases (oracles, liquidations, fee logic, rounding, MEV conditions)
Audits also became a credibility signal. Some teams won’t take integrations seriously unless there’s an audit report + a retest + a clear response plan.
If you’re seeing “AI audit review” in job descriptions, sanity-check it here:
Smart contract audit + AI review in JDs — legit workflow or marketing?
https://artofblockchain.club/discussion/smart-contract-audit-ai-review-in-jds-legit-workflow-or
Salary Breakdown for Auditors & Related Roles (2025)
Salaries in security vary more than people expect. A “title” doesn’t guarantee a range — the comp depends on proof, responsibility, and whether you’re doing high-stakes mainnet work versus smaller scoped reviews.
Auditors (rough patterns you’ll see reported):
Senior auditors in well-funded teams are often reported in high ranges, especially when leading retests and owning critical reviews.
Mid-level auditors vary widely depending on location, contract type, and whether the team pays mostly cash or includes token upside.
What makes comp vary the most:
Cash vs tokens: token-heavy packages can look big on paper and disappoint later
Reputation / public proof: recognizable writeups, contest history, clear reporting quality
Scope & responsibility: leading a retest and owning fixes is different than “running tools”
Specialization: formal verification, multi-chain, Cairo/Rust, ZK exposure can change your ceiling
If you’re evaluating token-heavy offers, read this thread before you accept:
Web3 job offer assessment: token compensation
https://artofblockchain.club/discussion/web3-job-offer-assessment-token-compensation
Read our discussion thread Web3 Job Offer Assessment: Token Compensation
What Makes Salaries Vary
Several factors affect how much you can earn:
Geography — Salaries are higher in the USA, Western Europe, Singapore etc. If you work remote for a US or EU project, you may get pay closer to those levels.
Experience & Reputation — Having public audits, a strong GitHub record, and known bug bounty wins helps a lot.
Organization Type — Startups may offer lower base but more token/equity upside. Established protocols or audit firms often pay higher base.
Special Skills — Formal verification, multi-chain auditing, knowledge of Rust / Cairo / Vyper etc., or ability to audit zero-knowledge proofs are rare skills that boost pay.
To support these numbers:
Metana Web3 Developer Salary Report (2025) gives ranges for protocol engineers and full-stack Web3 developers.
Cointelegraph’s “Highest Paying Jobs in Crypto 2025” article lists smart contract auditing as among the top roles.
Algorand Foundation Job Outlook Report shows average pay in U.S. markets for blockchain developers.
Skills, Tools & Qualifications You Need
A smart contract auditor isn’t “just a coder.” You’re basically paid to be calmly paranoid — to find failure paths before attackers do.
Before an audit even starts, strong teams expect:
a written spec (what the system should do)
a threat model (what can go wrong + who can do it)
a clear roles/admin model (who can change what)
tests that cover critical paths
a dependency list (tokens/oracles/routers/bridges)
a retest plan after fixes
Core technical skills:
Solidity (and depending on ecosystem: Rust/Cairo/Vyper)
security concepts: reentrancy, flash-loan style manipulations, access control failures, oracle assumptions
testing mindset: fuzzing, invariant tests, property-based thinking
code review discipline: reading intent, not just syntax
Tools auditors commonly use (but don’t worship):
Slither (static analysis)
Echidna (fuzzing)
Foundry (testing/invariants)
MythX/Manticore/Certora-style tools (depending on team maturity)
contest platforms: Code4rena, Sherlock
bounties: Immunefi
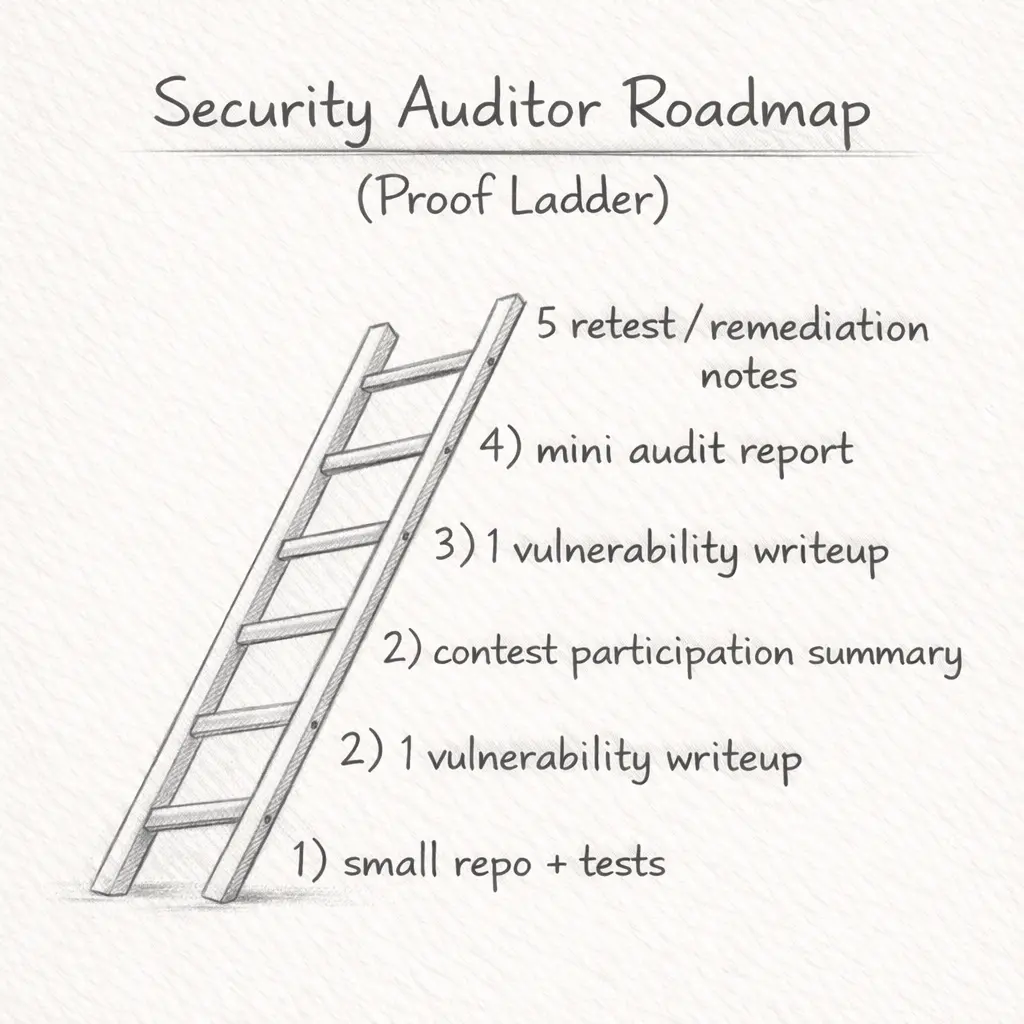
What counts as “real proof”:
clean repos with tests + clear readmes
writeups of vulnerabilities (even small ones) and what you learned
contest participation summaries (what you missed, how you improved)
at least one end-to-end mini audit writeup (scope → findings → fixes)
Career Path: Entry → Mid → Senior in Smart Contract Auditing
A lot of auditors didn’t start in blockchain. Many came from QA, cybersecurity, backend engineering, or even finance/risk. The path is open — but it rewards consistent proof.
Entry-Level (0–2 years):
What you do: write small contracts, learn testing discipline, run tools with understanding, assist reviews, write clean issue notes.
Milestones: a GitHub portfolio, 2–3 writeups, one contest participation summary, one tiny “mini audit” post.
Tip: if you’re coming from QA/security, position your transferable skills (test design, exploit thinking, systematic debugging).
If you’re getting rejected, this is usually why (and how to fix your proof):
Rejected for a smart contract auditor job — what should I put in my CV/portfolio?
https://artofblockchain.club/discussion/rejected-for-a-smart-contract-auditor-job-what-should-i-actually-put-in
Mid-Level (2–4 years):
What you do: lead smaller audits, own report quality, validate fixes, write better tests/invariants, start multi-chain exposure.
Milestones: published reports (or public writeups), repeated contest participation, stronger threat models, cleaner triage discipline.
Senior / Specialist (5+ years):
What you do: lead high-value protocol audits, mentor, design security processes, review upgrade patterns, define best practices, coordinate disclosure and post-mortems.
Milestones: recognized work, research output, repeated high-impact findings, leadership credibility.
Where the Work Is: Who’s Hiring in 2025
Where the Work Is: Who’s Hiring
Security work shows up in a few consistent places:
1) Audit firms
They hire across levels, often remote, and the learning curve is steep (in a good way). You’ll also get exposed to many codebases quickly.
2) DeFi protocols / DAOs
These teams need audits for upgrades, integrations, and ongoing monitoring. Security becomes part of shipping, not a “one-time event.”
3) Layer-1 / Layer-2 ecosystems
Scaling and new execution environments bring new risk classes. If you can reason about correctness + incentives, you’ll be valuable here.
4) Enterprises + fintech entering on-chain rails
Security + compliance-heavy environments where strong process matters.
5) Contests + bounties (freelance entry path)
Great for proof-building, but don’t treat it as guaranteed income early on. Treat it like structured practice with upside.
How to Land Your First Role
Breaking in feels overwhelming because “auditing” sounds like a senior-only role. The shortcut isn’t more courses. It’s clearer proof.
Start with small contracts and publish them with tests. Then build an “audit proof ladder”:
1–2 vulnerable-contract writeups (what broke + why)
one repo showing tests/invariants you wrote
one contest participation summary (even if you don’t win)
one clean writeup explaining what you missed and how you improved
That pattern shows maturity fast.
Also: be visible in the right places. Posting progress in communities makes it easier to get feedback and opportunities:
https://artofblockchain.club/discussion/smart-contract-security-audits-hub
Challenges & How to Overcome Them
1) High competition for entry roles
Security roles demand proof. Solution: publish small proof repeatedly — don’t wait for “perfect.”
2) Compensation volatility
Token-heavy comp can be risky. Solution: negotiate a stable base where possible and treat token upside as upside.
3) Quality gaps in audits
Some audits are shallow. Solution: build your personal standard: clear spec, tests, manual review, readable reporting.
4) Continuous learning pressure
The stack evolves fast. Solution: a weekly routine: read one post-mortem, do one small writeup, improve one repo/test.
Future Outlook & Trends in Blockchain Careers
AI-assisted auditing will continue to improve, particularly in pattern detection and faster triage. But AI doesn’t replace the hard part: reasoning about intent, incentives, integration risk, and edge-case behavior.
ZK and cryptography-heavy work will keep growing — and it will pull security expectations upward. Even if you don’t become a ZK specialist, learning how to think about proof systems and trust boundaries will help.
Compliance and security are also converging in many teams. You’ll see more “audit readiness,” “controls,” and “risk” language in job descriptions — especially when teams touch stablecoins, custody, or real-world integrations.
The biggest stable advantage remains the same: public track record + clear thinking. Recruiters and founders often check repos, writeups, contest footprints, and how you explain risk. That’s the signal.
For staying current, this thread is useful:
Smart contract security news: best sources and experts to follow
https://artofblockchain.club/discussion/smart-contract-security-news-best-sources-experts-to-follow-for-real-time
FAQs: Smart Contract Auditing Careers
Q1. Is smart contract auditing only for coders?
Not only, but you do need real Solidity skills to audit smart contracts properly. Many people enter Web3 security roles from cybersecurity, QA, or backend engineering, then build proof through smart contract audit checklist practice, code review, and testing. If you can explain reentrancy defense, access control, and threat modeling with examples, recruiters treat you as “audit-ready,” even without a perfect “security researcher” title.
Q2. How much can a smart contract auditor earn in 2025/2026?
Smart contract auditor salary varies by team maturity, chain ecosystem, and whether compensation is USD vs token-heavy packages. Senior Web3 security roles often pay higher when you own audit reports, retests, and incident response readiness. Mid-level auditors usually earn less but can add upside through bug bounties and audit contests. Always evaluate cash vs token mix, scope, and retest clauses before accepting.
Q3. Do I need a certification to get into auditing?
A certification can help with confidence, but it rarely beats proof. Most hiring teams judge Web3 security candidates by GitHub repos, audit writeups, contest history (Code4rena/Sherlock), and how you explain a smart contract audit process. If your portfolio shows clear findings, mitigation logic, and test coverage (Foundry/Echidna style), you’ll outperform candidates with only certificates and no public smart contract security track record.
Q4. What is the best way to start if I’m a beginner?
Start with one small Solidity repo and treat it like an “audit lab.” Write unit tests, add invariants, and document a smart contract audit checklist you followed. Then publish 1–2 vulnerability writeups (reentrancy, access control, oracle assumptions) and join one audit contest to learn real triage. Beginners who show consistent Web3 portfolio projects and clear security reasoning get interviews faster than “course-only” profiles.
Q5. Are these jobs remote-friendly?
Yes, many Web3 security roles and smart contract auditor jobs are remote, but remote rarely means timezone-free. Teams often expect overlap with US/EU hours, especially for audit retests, incident coordination, and release deadlines. Ask whether the role is US-only remote vs global, whether pay is USD/USDC, and what the escalation expectations are. Clear terms reduce burnout and compensation disputes.
Q6. How is AI changing blockchain careers and audits?
AI-assisted audits can speed up static analysis, pattern detection, and report drafting, but they don’t replace manual reasoning. The hardest bugs are logic flaws, economic exploits, and integration assumptions that break under edge cases. In 2026, strong auditors use AI tools plus Foundry/Echidna workflows, then validate findings with human threat modeling. Learning “AI + audit process” helps, but proof quality still wins hiring decisions.
Q7. Where can I network with professionals in this space?
Network where proof is visible. Join audit contest communities (Code4rena, Sherlock), bug bounty platforms (Immunefi), and technical forums where people review writeups and remediation. Security-focused Discords and hackathons help, but your strongest networking asset is a public track record: repos, audit notes, and post-mortems. Recruiters often scan “web3 security roles” candidates by links first, then CV later.
Q8. What should I prepare before paying for a smart contract audit?
Before you hire an audit firm, prepare a written spec, threat model, roles/admin keys, upgrade plan, dependency list (tokens/oracles/routers), and a clean test suite. Include deployment scripts and a retest plan so fixes are verified. This smart contract audit readiness package reduces audit cost, reduces back-and-forth, and improves report quality. It also helps you determine whether an auditor is conducting a genuine manual review or merely relying on tool output.